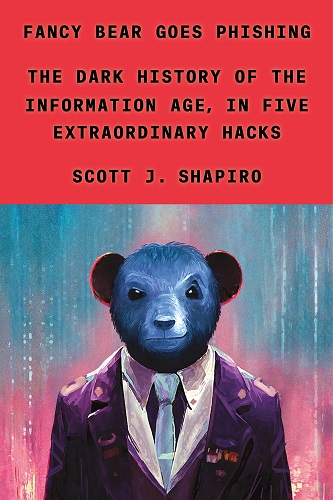
Fancy Bear Goes Phishing – The Dark History of the Information Age, in Five Extraordinary Hacks – Scott J. Shapiro
English | Tutorial | Size: 10.21 MB
Cybersecurity books, of which there are many, tend to fall in one of two camps. Either they have a joyless, eat-your-vegetables style or a breathless, run-for-the hills-now one. Fancy Bear Goes Phishing seeks to avoid both extremes. It is not a manual or user guide, nor is it a work of dark prophecy. My hope is that it will empower readers by equipping them to answer the three questions that sparked my own interest in this topic: Why is the internet so vulnerable? How do hackers exploit its vulnerabilities? What can companies, states, and the rest of us do in response?
DOWNLOAD:
Leave a Reply